At the worst possible time, millions of students and educators found themselves locked out of Canvas, the digital backbone of classrooms across the country. What started as a cybersecurity incident quietly detected in late April 2026 exploded into one of the largest educational data breaches on record, hitting right as schools entered finals season.
Canvas is a cloud-based learning management system (LMS) operated by a company called Instructure. It is a digital hub where teachers post assignments, students submit work, grades are recorded, and classroom communication happens. Its reach is enormous. Canvas counts more than 30 million active users globally and serves over 8,000 institutions as customers. In North America alone, it is used by 41% of higher education institutions, alongside thousands of K-12 schools. When it goes down, millions of people feel it immediately.
The incident did not appear out of nowhere. Instructure first detected unauthorized activity on April 29, 2026, and began an internal investigation. For a few days, the situation seemed contained. Then, on May 7, everything changed.
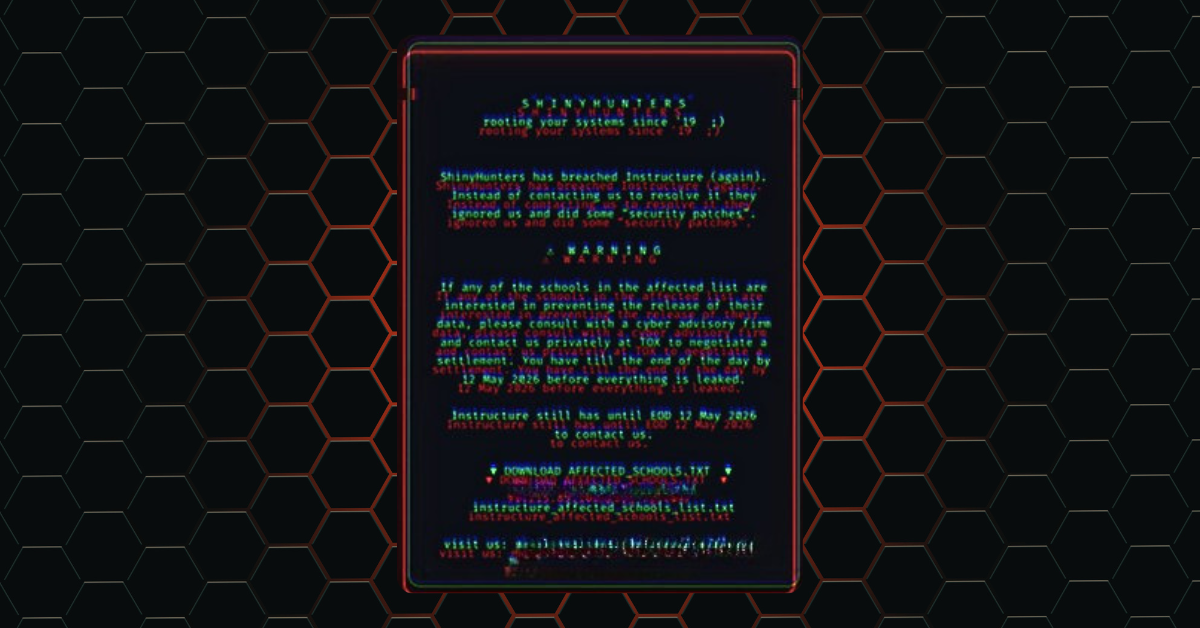
Students logging into Canvas around 1�20 p.m. PDT found something unexpected on their dashboards: a ransom note. The message was signed by ShinyHunters, a well-known criminal hacking group, and it was blunt. It claimed the group had breached Instructure, accused the company of ignoring earlier contact attempts, and threatened to release all stolen data unless affected schools negotiated a ransom settlement through the encrypted messaging platform Tox by the end of May 12, 2026.
“Instead of contacting us to resolve it, they ignored us and did some ‘security patches,’” the group wrote on user dashboards.
Instructure took Canvas offline shortly after to contain the damage. The outage disrupted access during a critical period, leaving students and faculty at thousands of colleges and K-12 schools scrambling for course materials, assignments, and communications.
ShinyHunters claimed to have stolen 3.65 terabytes of data tied to approximately 275 million users across roughly 9,000 institutions worldwide. The list of affected schools included major universities like Columbia, Princeton, Harvard, and Georgetown, as well as large public school systems across the country.
The breach is considered the largest educational security incident on record by scope and scale. According to Instructure’s own investigation, the stolen data included:
• Names, email addresses, and student ID numbers
• Private messages exchanged between students and teachers
Instructure stated it found no evidence that passwords, dates of birth, government identification numbers, or financial information were compromised. That is meaningful, but the exposure of private messages and identifying information is still significant, particularly given how personally sensitive communications between students and educators can be.
Instructure issued an apology on May 11 and updated its status page to note that Canvas was back online with no indication of ongoing unauthorized activity. On May 12, the company announced that the stolen data had been “returned” following an agreement with the hackers.
Cybersecurity experts were quick to note that “returned” data does not mean deleted data. There is no reliable way to confirm that copies were not made or retained before any handover.
Instructure notified impacted organizations on May 5 and has advised that affected schools will be contacted directly. For students, parents, and staff, the school or institution itself is the recommended first point of contact. The company is also organizing a leadership webinar to share further details about the attack and steps taken to harden its systems.
If you use Canvas through a school or university, take these steps:
• Enable Multifactor Authentication (MFA) on your Canvas account and any other school platform that offers it. This single step dramatically reduces the risk of unauthorized access even if your credentials were exposed.
• Be skeptical of unexpected emails or messages referencing your Canvas account, your school, or this breach. Phishing attempts often follow major incidents and can be convincingly detailed when attackers already have your name and email address.
Schools and IT administrators should rotate Canvas integrations, API keys, and single sign- on connectors, and review authentication logs for unusual activity between April 25 and May 8, 2026, per guidance from both Instructure and the Federal Student Aid office.
The Canvas breach is a reminder that education technology has become critical infrastructure, and critical infrastructure is a target. When a single platform serves 41% of North American higher education, a single point of failure becomes a national-scale event. The timing compounded the damage. Finals week is the highest-stakes period of the academic calendar. For students preparing for exams, submitting final papers, or trying to reach professors, even a few hours of outage created real consequences.
The breach raises important questions about how much sensitive communication is flowing through third-party platforms, and what obligations companies like Instructure have to protect it. Private messages between students and teachers were never meant for anyone else. That data is now out in the world in some form, regardless of what “returned” officially means. Stay alert, update your account security, and watch for follow-up communications from your school’s IT department.
Valley Techlogic plans include cyber security support and prevention, and we have worked with those in educational space to create customized solutions that take student safety in mind (including content filtering, strategies to protect student data privacy, device security and more). Learn more about our security as a service solutions here.

Looking for more to read?
- New malware dubbed “NoVoice” infiltrates the Google Play Store and infects 2.3 million devices
- .corn or .com? Domain scams are getting trickier, here’s how you spot them
- Social engineering scams on Facebook, LinkedIn and Twitter are increasing: what to look out for
- Five IT questions your MSP should be able to answer TODAY, and what it means if they can’t
This article was powered by Valley Techlogic, leading provider of trouble free IT services for businesses in California including Merced, Fresno, Stockton & More. You can find more information at https://www.valleytechlogic.com/ or on Facebook at https://www.facebook.com/valleytechlogic/ . Follow us on X at https://x.com/valleytechlogic and LinkedIn at https://www.linkedin.com/company/valley-techlogic-inc/.