CISA which stands for Cybersecurity & Infrastructure Security Agency is a federally recognized and funded cybersecurity agency that works to protect the United States from cyber threats, their mission statement reads:
“We lead the national effort to understand, manage, and reduce risk to our cyber and physical infrastructure.”
CISA collects, analyzes, and shares threat intelligence so organizations can act before damage occurs. This includes vulnerability alerts, Known Exploited Vulnerabilities (KEV) catalog updates, and joint advisories with partners like the FBI and NSA. The goal is simple: shorten the time between “threat discovered” and “defenses updated.”
Now due to federal cuts initiated by the Trump administration they’re operating at just 38% of their necessary staffing levels, these cuts included staff that worked under programs such as the counter-ransomware initiative and one that oversaw efforts to promote secure software development. Many of their employees were also reassigned to other agencies such as the Department of Homeland Security as funding and efforts are shifted to the administration’s immigration crackdowns.
CISA has also been without a permanent director since Trump took office, leaving the agency both without the necessary manpower and crucial leadership guidance. While the agency continues to exist, it’s hard to ignore that these cuts may have a real time effect on our country’s national security. Business owners in particular should be wary of an increase in potential threat as bad actors may take advantage of this gap.
Cuts to government programs such as these can trickle down to business owners, the effects will not be immediate but sustained cuts to CISA can quietly increase cyber risk, slow federal support, and shift more responsibility (and cost) onto businesses and their MSPs. These are four trickle down affects you should be aware of:
1. Slower and shallower threat intelligence
CISA is one of the primary pipes pushing timely threat intelligence to the private sector. If funding drops, you often see:
- Fewer or slower vulnerability advisories
- Less frequent updates to the Known Exploited Vulnerabilities catalog
- Reduced joint analysis with FBI and NSA
- Less sector-specific guidance
Business impact:
Owners and MSPs get less early warning. That increases dwell time for attackers and raises breach probability over time.
2. Reduced free security services
Many organizations (including SMBs, schools, local governments, and some private entities) rely on CISA’s no-cost services such as:
- Cyber Hygiene scanning
- Vulnerability disclosure coordination
- Remote penetration testing (for eligible businesses)
- Phishing campaign assessments
If budgets tighten, these programs are often first on the chopping block or become capacity-constrained, leaving you optionless when you need their support.
Business impact:
- Fewer free scans available
- Longer wait times
- More reliance on paid security assessments
- MSPs must fill the gap
3. Weaker critical infrastructure resilience
CISA plays a coordination role across sectors like healthcare, energy, water, and transportation. Funding cuts can mean:
- Fewer field advisors
- Less regional engagement
- Reduced ICS/OT security work
- Slower cross-sector coordination
Business impact:
Even if you think of yours as “just a small business,” you depend on these sectors. Increased fragility upstream can mean:
- More outages
- More supply chain disruptions
- Higher cyber insurance pressure
- More third-party risk exposure
This is the second-order effect many owners miss.
4. Slower incident response support at scale
For large or multi-organization incidents, CISA helps coordinate national response. With fewer resources:
- Surge capacity drops
- Federal assistance may triage more aggressively
- Recovery guidance may lag during major events
Business impact:
Most business owners do not call CISA directly. But during widespread campaigns (think mass exploitation events), weaker federal coordination can mean:
- Longer active threat windows
- More widespread compromise
- Slower ecosystem-wide containment
The bottom line, cuts such as these carry consequences, some that you can anticipate and some that you can’t. Either way, it’s of the utmost importance that in 2026 you have protections in place that specifically cover your business from threat actors, regardless of what protections may be in place nationwide. All Valley Techlogic plans include cybersecurity protections (including 24/7 threat detection and monitoring) by default. Learn more today through a consultation.
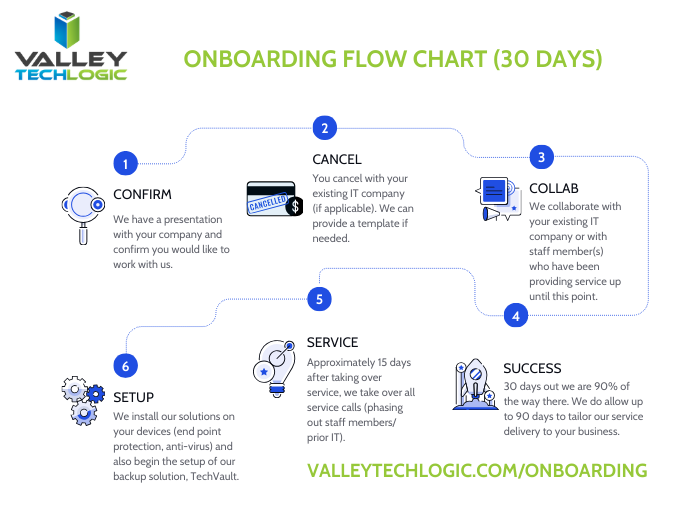
This article was powered by Valley Techlogic, leading provider of trouble free IT services for businesses in California including Merced, Fresno, Stockton & More. You can find more information at https://www.valleytechlogic.com/ or on Facebook at https://www.facebook.com/valleytechlogic/ . Follow us on X at https://x.com/valleytechlogic and LinkedIn at https://www.linkedin.com/company/valley-techlogic-inc/.